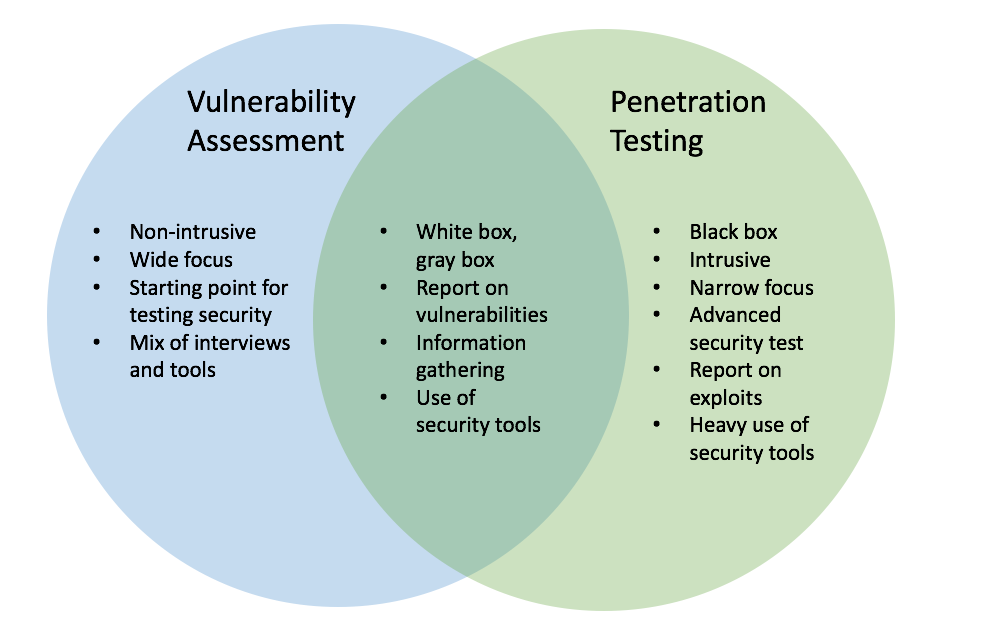
PENETRATION AND VULNERABILITY TESTING
A penetration test, colloquially known as a pen test, is an authorized simulated attack on a computer system, performed to evaluate the security of the system. The test is performed to identify both weaknesses (also referred to as vulnerabilities), including the potential for unauthorized parties to gain access to the system's features and data, as well as strengths, enabling a full risk assessment to be completed. The process typically identifies the target systems and a particular goal—then reviews available information and undertakes various means to attain the goal.
- Find an exploitable vulnerability.
- Design an attack around it.
- Test the attack.
- Seize a line in use.
- Enter the attack.
- Exploit the entry for information recovery.
Flaw hypothesis methodology is a systems analysis and penetration prediction technique where a list of hypothesized flaws in a software system are compiled through analysis of the specifications and documentation for the system.